How Your Instagram Account Can Be Hacked and How To Stop It
Instagram, one of the most popular social media platforms around the world, has become a major target for hackers in recent times. Instagram accounts can be hacked for various reasons, including stealing personal information, breaking into businesses, or gaining access to valuable data. In this article, we will discuss how Instagram accounts can be hacked and how to prevent such incidents.
How Your Instagram Account Can Be Hacked
There are several ways in which an Instagram account can be hacked, and here are some of them:
1. Phishing Attacks: This is a popular technique that hackers use to steal Instagram login credentials. They create fake login pages, emails, or messages that seem legitimate and request for login details. Once the user falls into the trap, their data is compromised.
2. Weak Passwords: A weak password can be easily guessed by hackers, and once they figure it out, they can access the account without any problem.
3. Social Engineering: Social engineering is the process of manipulating individuals into sharing their private information. For instance, a hacker may create a fake Instagram account and interact with the victim to gather information without their knowledge.
4. Third-Party Applications: Some third-party applications that require Instagram login credentials might store the information insecurely, allowing hackers to steal the information.
How To Stop Your Instagram Account from Being Hacked
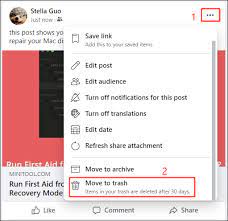
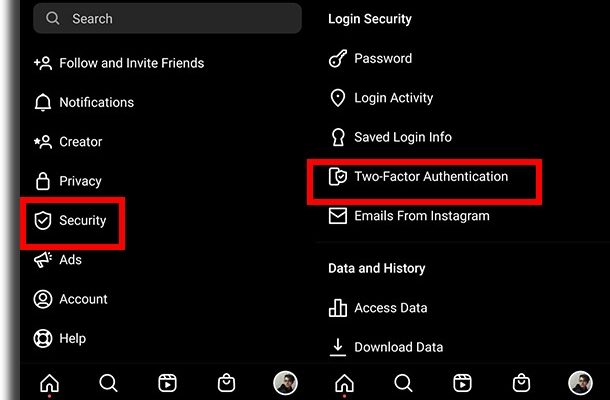
1. Two-Factor Authentication: Two-factor authentication is an added layer of protection that requires users to provide an additional login credential besides a password. This makes it more difficult for hackers to access the account.
2. Strong Passwords: Users should create strong passwords that include a combination of uppercase letters, lowercase letters, numbers, and special characters. This makes it more difficult for hackers to guess the password.
3. Avoid Suspicious Links: Users should refrain from clicking on suspicious links, messages, or emails asking for their Instagram login credentials.
4. Use Trusted Third-Party Applications: Users should only use trusted third-party applications that have been vetted by Instagram.
5. Keep Your Instagram App and Operating System Up-to-Date: Hackers often exploit vulnerabilities in outdated versions of the Instagram app and operating system. Keeping them up-to-date can prevent such exploits.